Architecting build-time microfrontends for scale, integration, and team autonomy

Posted By
Sachin Warke

In the earlier blog on build-time microfrontends for scalable frontend systems, we covered what build-time microfrontends are, how static composition works, and why this model trades deployment flexibility for integration confidence. If you haven't read that yet, it's the best place to start before diving into architecture. The next step is understanding how this translates into a real system — not the theory, but the concrete architectural structure that teams design, build, and operate day to day.
In this blog, I'll walk through the core components of a build-time microfrontend platform, how static composition is achieved through package-based integration, how routing and authentication are handled without dynamic loading, and how shared dependencies are managed safely across independently owned packages. For the runtime equivalent, see our post on runtime microfrontend architecture.
What are the core system components of a build-time microfrontend platform?
A build-time microfrontend platform is built around clearly defined roles. Each component has a specific responsibility, and keeping those boundaries intact is what allows teams to work independently while still producing a coherent, integrated frontend.
Core architectural elements of build-time microfrontends
| Component | Responsibility |
|---|---|
| Container Application (Shell) | Owns top-level routing, authentication, layout, and assembles all microfrontend packages at build time |
| Microfrontend Packages | Independently developed, versioned npm packages, each owning a distinct UI domain or product area |
| Shared UI Library | Versioned design system and common components, published as a peer dependency consumed by all packages |
| Shared Utility Modules | Common services — API clients, auth context, feature flags, telemetry — published as shared peer dependencies |
| Package Registry | The artifact store (npm, Verdaccio, Artifactory) where published microfrontend package versions are hosted and resolved |
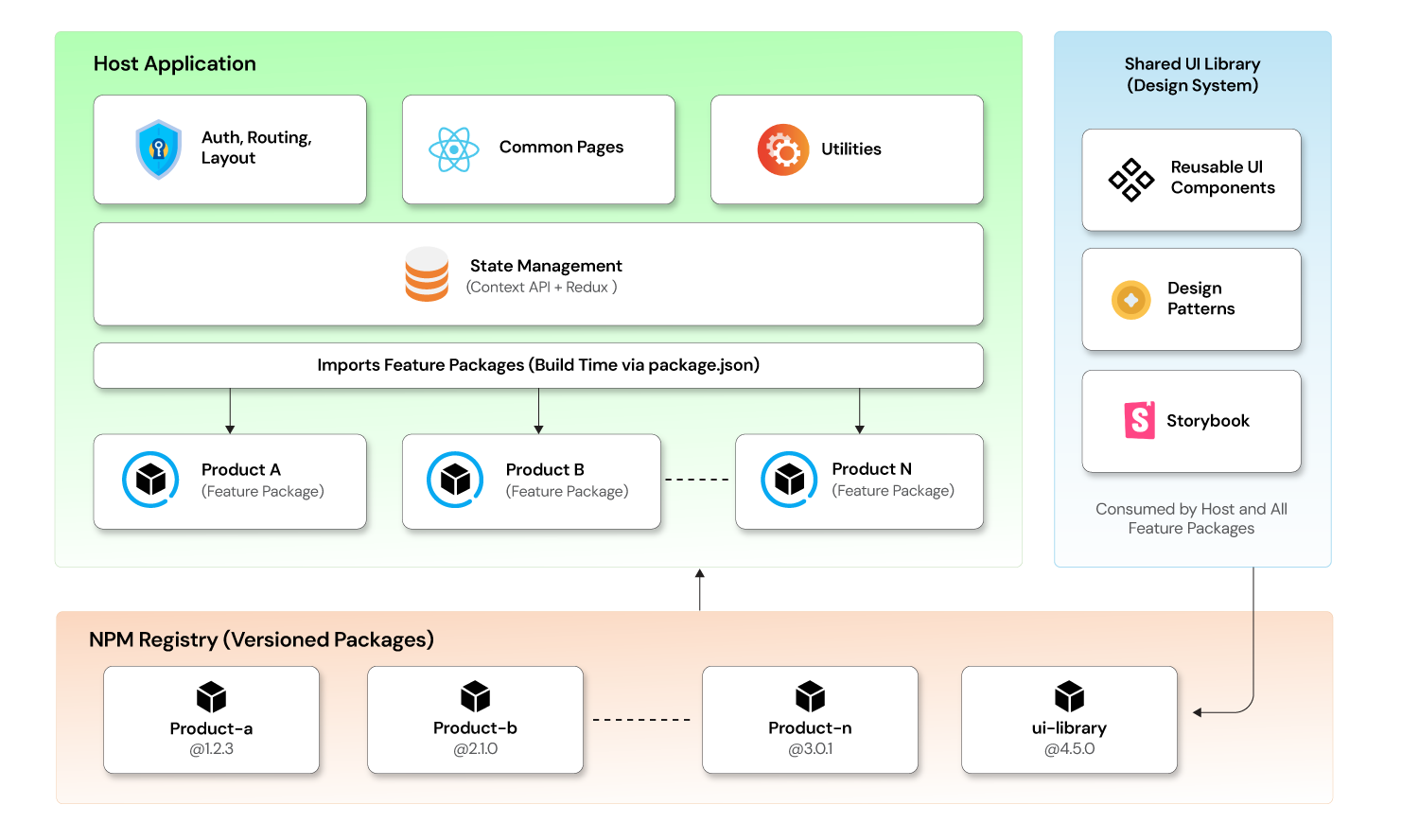
Domain logic lives inside microfrontend packages. Platform logic — routing, session handling, layout — lives in the container and shared libraries. When those lines blur and packages start reimplementing platform concerns, teams lose isolation and build-time conflicts become harder to diagnose. This is the most common anti-pattern in poorly structured build-time microfrontend systems. The best architectures treat this boundary as a first-class constraint enforced from day one — not something teams clean up after the fact.
How does build-time composition and pipeline orchestration work?
Build-time microfrontends shift integration from the browser into the build pipeline. This requires a structured, version-aware composition model that produces a verified, deployable artifact before anything reaches production.
How does static integration work with package-based microfrontend composition?
Most production build-time microfrontend implementations rely on a package registry combined with a bundler — webpack, Vite, or Rollup — to pull versioned microfrontend packages into a single build. Each microfrontend exports its components and routes as a standard npm package. The container declares exact version dependencies and imports them directly.
The integration flow typically looks like this:
- Container's package.json declares each microfrontend package with a pinned or range-locked version
- The build system resolves all package versions from the registry, with lockfile enforcement ensuring reproducibility
- The bundler processes the full dependency graph — including every microfrontend package — applying tree shaking, code splitting, and minification across the entire output
- The result is a fully integrated, deployable frontend artifact where every UI module is already present and verified
This is what gives build-time composition its core value. The bundle that exits the pipeline is the exact bundle that runs in production. There are no remote fetches, no version resolution at runtime, and no integration surface that wasn't already exercised during the build.
What should the container own in a package-based build-time architecture?
In build-time microfrontend setups, the container is not where product features live. It operates as the integration and platform layer, responsible for:
- Declaring and resolving all microfrontend package versions
- Defining the top-level route structure and rendering the correct package per route
- Managing authentication, session state, and user context
- Providing shared context providers that downstream packages consume
- Running the integrated build and producing the deployment artifact
Keeping the container thin prevents it from becoming a second frontend monolith. If product features start accumulating inside the container, the architecture loses its primary advantage: the ability to own, develop, and publish microfrontend packages independently.
How are routing, authentication, and cross-package communication handled in build-time microfrontends?
Build-time composition only works cleanly when platform concerns are centralized in the container and domain logic stays inside packages. Routing and auth are the two areas where this discipline matters most.
Routing strategy
The container owns all top-level routes, declared statically in its routing configuration:
/dashboard
/product-a/*
/product-b/*
When a route is matched, the container renders the corresponding microfrontend package's root component. Each package then manages its own internal routing independently. Since everything is bundled at build time, route-based code splitting is handled by the bundler rather than by a dynamic loader. The result is the same user experience — the right UI for the right route — but without any runtime module fetching.
How is authentication handled centrally across build-time microfrontend packages?
Users authenticate through the container, which manages session tokens and exposes identity context to packages through shared context providers or a shared state module. Packages consume user identity through a well-defined interface — typically a React context, a Zustand store slice, or a shared auth utility module published to the registry.
Packages do not implement separate login mechanisms or make independent auth decisions. This is critical for both security governance and for avoiding the scenario where different packages operate on different session states simultaneously. In build-time microfrontend architecture, centralizing auth in the container is non-negotiable.
What is the best approach to shared state in a build-time microfrontend system?
Some state needs to cross package boundaries — user preferences, selected tenant context, notification counts, or global feature flag evaluations. In build-time systems, this is typically handled through:
- A shared state package (a Redux store with defined slices, or a Zustand store) that each microfrontend imports as a peer dependency
- A shared event bus module for loosely coupled cross-domain notifications
- Framework context providers initialized in the container and passed down through the React tree
The principle is the same as in runtime systems: share only what genuinely needs to cross domain boundaries. Private state stays inside the package that owns it. Overusing the shared state surface creates tight coupling between packages and defeats the purpose of domain isolation.
How do top engineering teams manage dependencies and ensure build stability?
Static composition solves one class of dependency problems — runtime version conflicts — but introduces others that require deliberate management at the package and pipeline level.
How do you manage shared dependencies and avoid bundle duplication?
The most critical dependency concern in build-time microfrontend architecture is bundle deduplication. If the container and each microfrontend package bundle their own copy of React, your final output carries redundant weight and risks subtle runtime inconsistencies between instances of the same library.
The standard approach is to declare shared, singleton libraries — React, React DOM, React Router, your design system — as peer dependencies in each microfrontend package, and let the container own the actual dependency declaration and version resolution. This ensures the bundler resolves a single instance of each shared library across the entire build, regardless of how many packages reference it.
Teams enforce this through peer dependency declarations in package.json, automated peer dependency checks in CI, and bundler configuration that externalizes known singletons. Build tools like Nx and Turborepo add affected-build detection on top of this, so a change in one microfrontend package triggers rebuilds only for the container and the packages that actually depend on it — not the entire system. For engineering leaders, this is one of the top reasons to invest in build tooling early — the cost of retrofitting dependency governance into a mature system is significantly higher than getting it right from the start.
What observability and quality gates should a build-time microfrontend CI pipeline include?
In runtime microfrontend systems, production failures during remote loading are a real operational risk. Build-time composition eliminates that specific failure mode, but replaces it with a different observability requirement: you need strong signals from your build pipeline before anything reaches production. A well-designed CI/CD pipeline is what makes this model work in practice.
Production build-time microfrontend systems implement:
- Automated integration tests against the assembled artifact: End-to-end tests and visual regression tests run against the fully built and integrated container, not just against isolated packages
- Dependency audit steps in CI: Aautomated checks catch peer dependency violations, unexpected duplicate packages, and version range conflicts before the build completes
- Bundle size monitoring: Since all packages contribute to a single output, bundle size budgets and size regression checks protect against packages adding unintended weight to the shared artifact
- Deployment pipeline gating: The container does not deploy unless all integration tests, dependency audits, and size checks pass — the build pipeline is the quality gate, not production monitoring
Without this CI discipline, the build-time model's primary advantage — verified integration before deployment — is partially wasted.
Why does build-time microfrontend architecture matter for enterprise-scale frontend delivery?
Build-time microfrontends scale well not because of any specific toolchain, but because the architecture aligns technical integration boundaries with what teams actually need: a verified, stable surface to deliver against. Each team owns and publishes its package independently. The container integrates everything through a controlled, auditable build process. Failures stay local to the team that introduced them — and they're caught in CI, not in production.
At the same time, sharing UI components, state, and utility modules through well-maintained peer dependencies keeps the user experience consistent across the product without requiring teams to coordinate on every release. The container stays thin, packages stay focused, and the build pipeline carries the integration burden that would otherwise fall on runtime infrastructure.
With strong dependency governance and a disciplined CI pipeline, a build-time microfrontend architecture lets frontend systems grow without accumulating hidden coupling or unpredictable deployment risk. This is particularly relevant for organizations in regulated industries, enterprise environments, or any product domain where a broken UI in production has direct business consequences. For those teams, build-time microfrontend integration is not a compromise on deployment speed — it's a deliberate choice to front-load integration verification where tooling can handle it, rather than discovering problems in the browser. If your organization is in the middle of modernizing a legacy frontend system, Opcito's software product engineering and application modernization teams have done this work across a range of frontend scales and delivery models.
Designing build-time microfrontends that scale requires careful decisions across package boundaries, pipeline design, and shared dependency governance. At Opcito, we help engineering organizations implement production-ready microfrontend platforms built for long-term stability and team autonomy. To discuss your architecture and next steps, connect with Opcito's microfrontend experts.
















